The promise of the decentralized VPN—a network of low-power, edge-computing relay nodes—remains one of the most alluring fantasies of the "liberated internet." By leveraging Raspberry Pis and the lean, kernel-space efficiency of WireGuard, individuals are theoretically capable of building their own privacy-preserving infrastructure. In 2026, however, the delta between the "DIY privacy hero" narrative and the reality of operating these nodes is wider than ever. Profitability is not found in bandwidth arbitrage; it is found in the niche, high-trust markets of decentralized infrastructure-as-a-service (IaaS), where the cost of uptime is human attention, not just hardware.
The Architecture of the DIY Relay: Why WireGuard Matters
In 2017, WireGuard was the challenger. In 2026, it is the incumbent, but its dominance is purely technical. While OpenVPN persists as a legacy anchor, WireGuard’s 4,000 lines of code have become the industry standard for lightweight tunneling. For a Raspberry Pi 4 or 5 deployment, this is critical. The bottleneck isn't the CPU clock; it’s the network stack management and the I/O overhead, a struggle for efficiency that also plagues firms as they pivot to The Post-Quantum Security Gold Rush: How Consultancies Are Preparing for 2026.
When you build a relay node, you aren't just running a script; you are becoming a micro-ISP. The operational reality is that once your node hits public DHT (Distributed Hash Table) trackers, your IP address becomes a target for automated vulnerability scanners. The "profit" aspect usually stems from participating in decentralized bandwidth sharing networks (like Mysterium or Sentinel). These platforms promise to turn your home fiber line into a passive income stream. The problem? Your residential IP is a "dirty" asset.
The "Residential IP" Paradox: Economic Reality
The primary reason to run a relay is the value of your ISP-provided IP address. Commercial data centers are often blacklisted by streaming services, banking apps, and anti-fraud systems like Cloudflare’s "I am under attack" screens. Residential IPs, conversely, are the "gold" of the proxy market.
However, if you offer relay services to anonymous users, you are essentially opening your network to any traffic that traverses your local loop. If a user utilizes your relay to perform malicious activity—phishing, DDoS attacks, or copyright infringement—it is your billing address and your ISP contract that will receive the cease-and-desist letter.
"I thought I’d make $50 a month with my Raspberry Pi relay. Then I got a call from my ISP because someone on the node tried to brute-force a government portal in Eastern Europe. The 'passive income' was less than the cost of the legal headaches." — User comment from a r/selfhosted thread, 2025.
This creates a high "Trust Tax." The profit is inherently limited by the risk you are willing to assume. To mitigate this, successful operators are moving away from open, anonymous relays toward private, tiered access models where they know their clients.
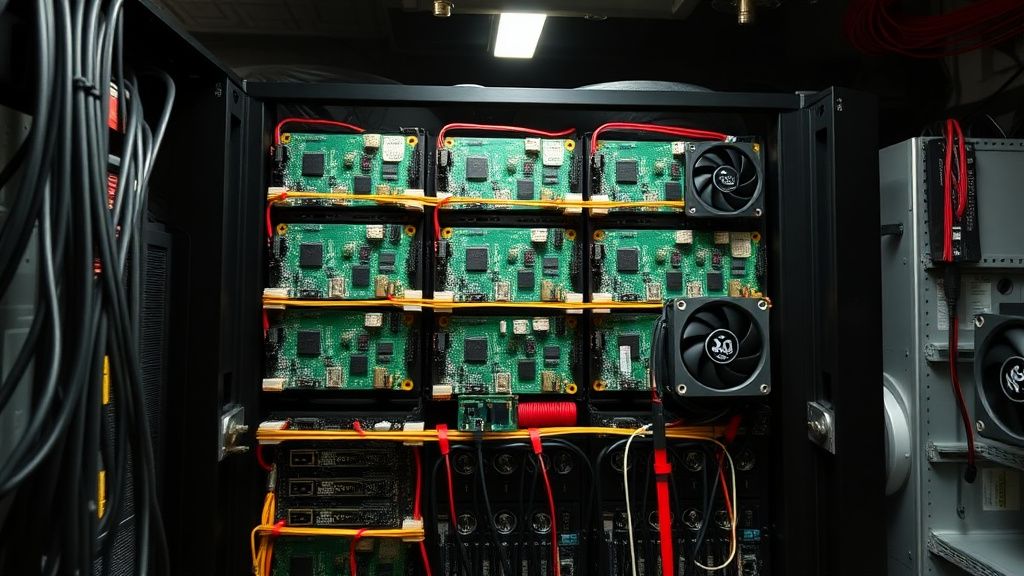
Field Report: The "Community Node" Experiment
In late 2025, a project in a mid-sized German city attempted to bridge the gap by creating a localized WireGuard mesh for a neighborhood association. They used a cluster of 10 Raspberry Pi 5 units, each acting as an exit node for a different regional gateway.
- The Success: The latency for local users was abysmal (sub-10ms), and the privacy protections were verified by local security researchers.
- The Failure: Scalability. Once the node count grew, the administrative overhead—managing keys, rotating credentials, and handling user support (the "why is my Netflix blocked" tickets)—became a full-time job.
The "profit" was not monetary; it was social capital and localized privacy. Monetization failed because the moment they tried to charge a monthly subscription, they became a regulated entity. The regulatory friction is the invisible wall that kills most "profitable" relay side-hustles, forcing entrepreneurs to look at more sustainable income models, such as the ones detailed in Turning Food Waste into Profit: How to Launch a Boutique Composting Business in 2026.
The Technical Debt of Scaling
Running a relay is easy. Running a reliable relay is a nightmare of "edge-case" management.
- MTU Issues: WireGuard packets have a different overhead than standard TCP/IP. If you don't configure your Maximum Transmission Unit (MTU) correctly, you will experience "stuck" connections where simple web pages load, but large file transfers or video streams time out. This is the #1 reason users drop off.
- IP Reputation Management: Your ISP might cycle your dynamic IP. If you don't have a robust DDNS (Dynamic DNS) client that updates your WireGuard peers instantly, your relay goes "dark."
- Kernel Panics: Raspberry Pis are not hardened servers. A power fluctuation or a corrupted microSD card—the common enemy of all Pi users—will bring your node down. You need a UPS, and you need a high-end, high-write endurance SD card or an external NVMe SSD.
Counter-Criticism: Why Experts Are Skeptical
Critics often point out that the "decentralized VPN" model is fundamentally flawed from a threat-modeling perspective. If you are routing your traffic through a random person’s Raspberry Pi, you have no guarantee that the operator isn't logging your traffic via tcpdump or injecting malicious headers into your HTTP requests.
The consensus in the infosec community is that a truly secure relay service requires a level of cryptographic auditing that a typical home-user simply cannot provide. Therefore, the "profit" often attracts actors who are incentivized to compromise the very security they are selling.
The Workaround Culture: When Infrastructure Fails
When the default WireGuard implementation hits the walls of a consumer-grade router's NAT, the community turns to "NAT Traversal" hacks—STUN/TURN servers, or more commonly, Tailscale (which abstracts WireGuard). While Tailscale makes the deployment "it-just-works" simple, it adds a central control plane.
You are trading the "total privacy" of raw WireGuard for the "operational stability" of a managed mesh. Is it profitable? Only if you are selling the solution (the managed networking) rather than the relay (the raw bandwidth).
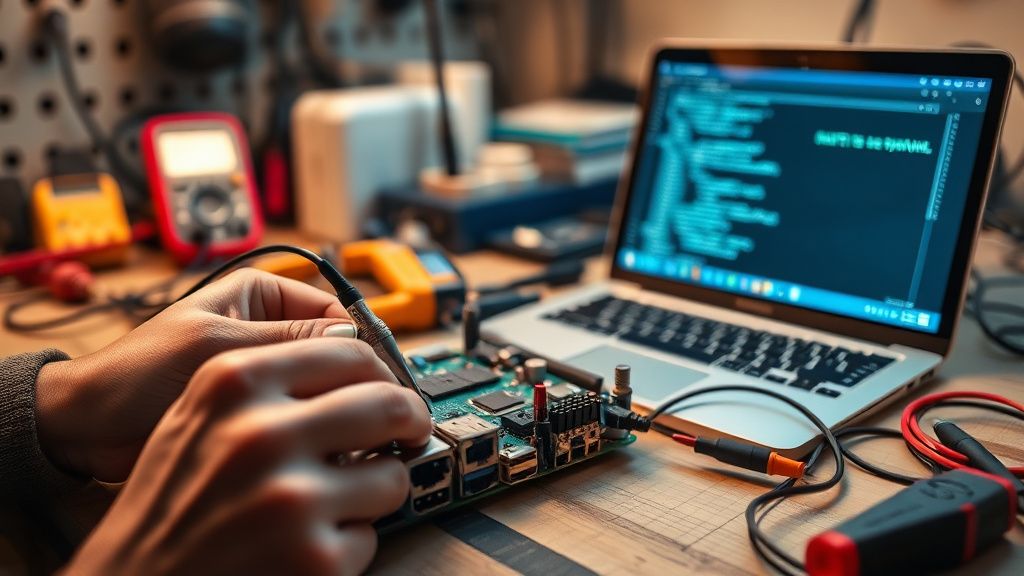
Roadmap to a Sustainable Operation
If you are determined to attempt this, abandon the idea of "passive income." Pivot to "managed infrastructure":
- Target Niche Clients: Instead of open relaying, sell private, dedicated VPN instances to small businesses or privacy-conscious individuals who need a dedicated exit node in your specific geographic region.
- The "Managed" Upsell: Charge for the setup and maintenance of their personal WireGuard mesh, not just the connection itself.
- Infrastructure Hygiene: Use automated backups (
rsyncto a secondary off-site location) and monitoring tools (Prometheus + Grafana). If your node goes down, you need to know before the client does.
How much can I actually earn running a relay?
In 2026, if you are contributing to bandwidth-sharing networks (like Mysterium), expect to earn significantly less than the electricity costs of keeping the device running. Profitability via these networks is effectively a myth; you are paying to support the network. If you monetize via private clients, income is based solely on your ability to handle customer support.
Is my ISP going to shut me off?
In many jurisdictions, yes. Residential Service Level Agreements (SLAs) almost universally forbid "hosting services" or "commercial use." If your node starts handling large volumes of traffic, your ISP's automated traffic analysis will flag your account for "commercial-grade usage on a residential line." Keep your traffic volume modest to stay under the radar.
Does WireGuard provide anonymity for the relay operator?
Absolutely not. WireGuard is a tunneling protocol, not an anonymization network like Tor. Your public IP is exposed to the peers you connect to. If you are running an exit node, you are essentially exposing your home network address to the entire internet. This is a massive security risk if not properly firewalled (use
iptablesornftableseffectively).
What is the most common point of failure?
Without question, the microSD card. Raspberry Pis are notoriously rough on flash storage. After six months of heavy logging and traffic, a cheap SD card will corrupt. Always use an industrial-grade card or, preferably, boot your Raspberry Pi from an external USB 3.0 SSD.
Why not just use a VPS in a datacenter?
Because the whole point of a "residentially-homed" relay is the IP reputation. Datacenter IPs are trivially easy to block. However, as noted in the field reports, this is exactly what makes the residential IP a "dirty" asset. The security trade-off is the single most debated topic in this space today; there is no "correct" answer, only the risk you are willing to accept.
